CCSS Audit
- IT Security Audit and Assessment
- Compliance Audit and Industry Requirements
- Initial and follow-up audit after corrective action
- Enhance information security and digital asset protection
What is CSCC?
CryptoCurrency Security Standard (CCSS) is a set of requirements for all information systems that make use of cryptocurrencies, including exchanges, web applications, and cryptocurrency storage solutions. By standardizing the techniques and methodologies used by systems around the globe, end-users will be able to easily make educated decisions about which products and services to use and with which companies they wish to align.
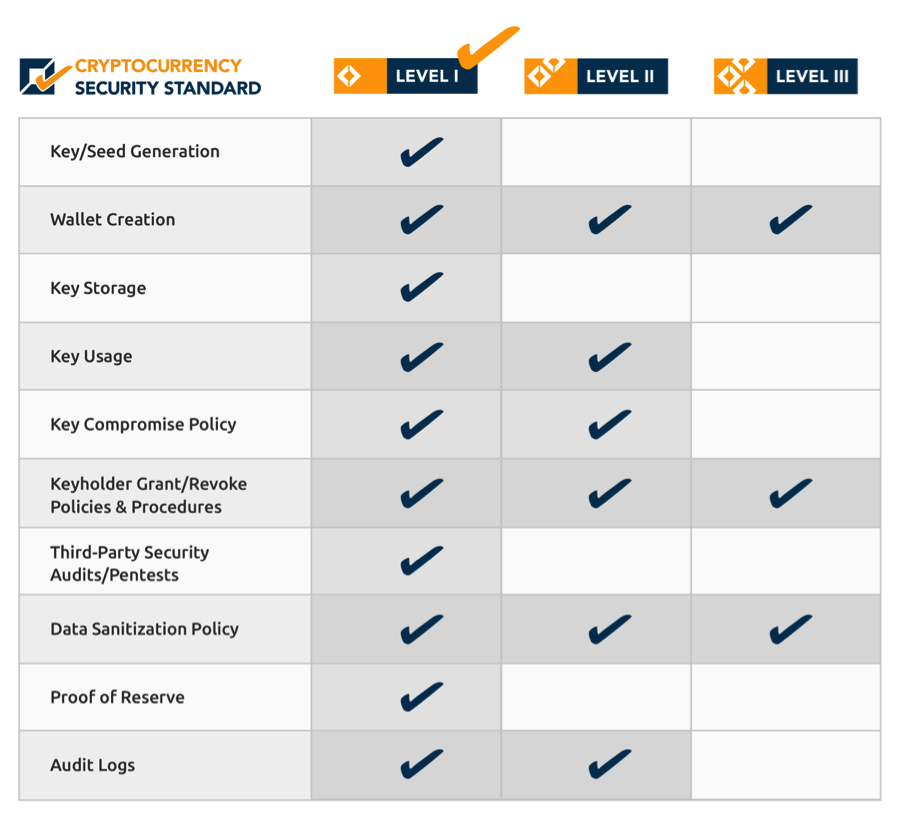
CSCC Audits Category
Cryptographic Asset Management
- Key / Seed Generation
- Wallet Creation
- Key Storage
- Key Usage
- Key Compromise Protocol (KCP)
- Keyholder Grant/Revoke Policies & Procedures
Operations
- Security Audits / Pentests
- Data Sanitization Policy (DSP)
- Proof of Reserve (PoR)
- Audit Logs
CCSS is broken into three (3) levels of increasing security. Details of these are outlined in this section.
Level I
An information system that has achieved Level I security has proven by way of audit that they protect their information assets with strong levels of security. Most risks to the system’s information assets have been addressed by controls that meet industry guidelines. While this is the lowest level within CCSS, it still represents strong security.
Level II
An information system that has achieved Level II security has proven by way of audit that they exceed strong levels of security with additional enhanced controls. In addition to covering most risks to the information system’s assets, the use of decentralized security technologies such as multiple signatures have been employed which exceed industry guidelines and provide redundancy if any one key or person becomes unavailable or compromised.
Level III
An information system that has achieved Level III security has proven by way of audit that they exceed enhanced levels of security with formalized policies and procedures that are enforced at every step within their business processes. Multiple actors are required for all critical actions, advanced authentication mechanisms ensure authenticity of all data, and assets are distributed geographically and organizationally in such a way to be resilient against compromise of any person or organization.